Ransomware cyberattacks have been increasing at an alarming rate recently, with the finance, technology, education, manufacturing, and healthcare sectors being the most affected. Ransomware groups typically target large corporations. However, the trend is shifting as the ransomware business evolves into a service (SaaS) model with sophisticated tools at its disposal. This broader accessibility of these tools lowers the technical bar for cybercriminals to launch attacks on organizations of any size from any part of the globe. But on the bright side, most targeted ransomware attacks take days, weeks, or even months to complete, from the initial compromise to the final data encryption phase.
Lateral Movement
Lateral movement is a technique cybercriminals use to progressively move from a compromised host to the rest of the network in the search for sensitive data to exfiltrate and encrypt to demand ransom. And any successful ransomware operation involves one or more lateral movements of the attacker in the network looking for critical systems and valuable data. So, preventing lateral movement is crucial for any organization to avoid becoming a victim of a ransomware attack.
Network Segmentation for Improved Security
One of the effective ways to secure networks from ransomware attacks is through network segmentation. Network segmentation divides the larger network into smaller ones with limited connectivity between them. However, the most effective way to secure networks, whether on-premises or in cloud environments, is to use a zero-trust architecture that extends security to the resource level instead of the network level. But as of this writing, there is no evidence that anyone has ever built a complete zero-trust solution.
Even Google’s BeyondCorp enterprise zero-trust implementation is very limited in scope – currently limited to web apps. Moreover, their implementation seems to have done little to encourage other organizations that rely on many legacy applications and protocols to switch to zero-trust architecture in the foreseeable future. Until then, many organizations might continue to use traditional network segmentation for security, possibly with some zero-trust overlay. Consequently, the following example assumes network segmentation with some form of packet filtering, especially with a Firewall.

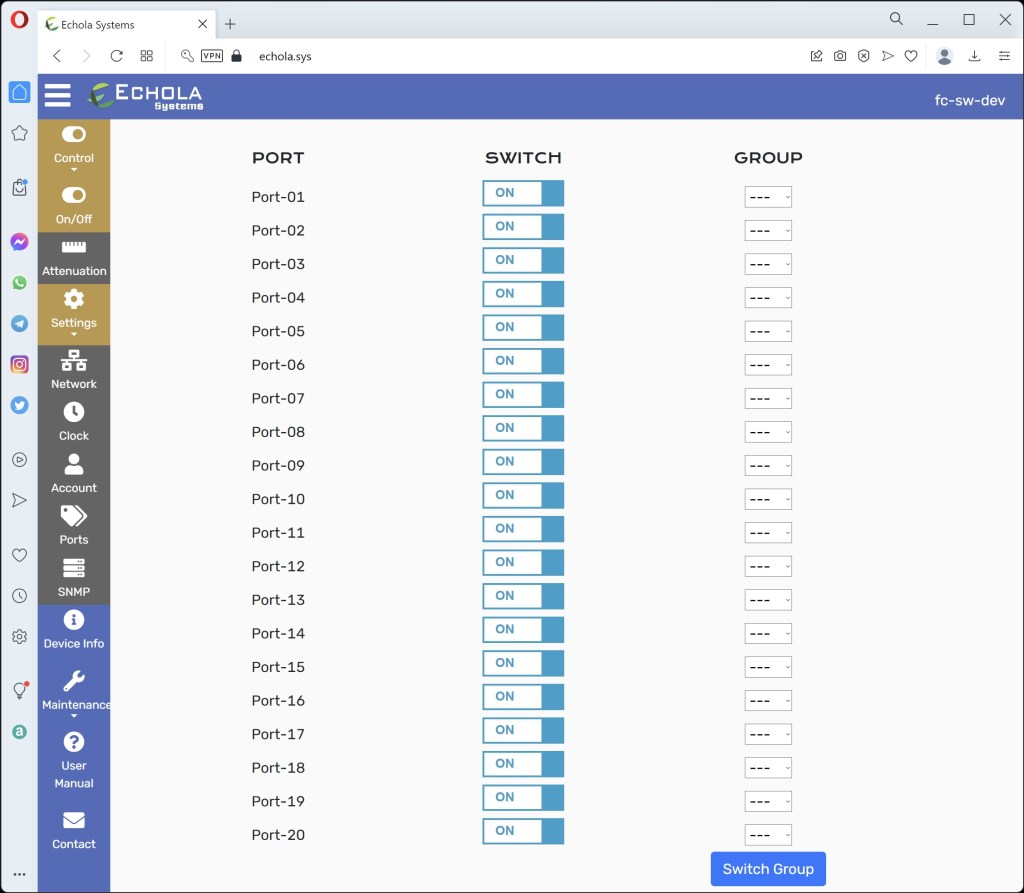
The Echola VFC2011 is a 20-port fiber-cut physical (L1) layer switch with small form-factor LC connectors. Each port can support up to 100G speed, and you would require two ports for each segment/interface. The Echola fiber-cut switch can also be used as an air-gap switch to provide isolation for your backups.
When the security team or a SIEM tool detects a threat, the fiber-cut switch can be activated to sever the communication between the affected and other segments to provide better containment. Thus it helps to limit the impact to one segment giving time for the security team to respond and mitigate the attack.
The fiber-cut kill switch offers the following benefits over traditional software isolation methods, which are vulnerable to ransomware exploitation.
Foolproof Isolation: The threat actors can not break into the optical switch as the optical interfaces are isolated from its control plane. It can only be accessed through an out-of-band channel.
Reduced Complexity: The fiber-cut switch does not require running complex policy scripts or disrupting equipment power cycling.
Faster Response: Instant isolation at the click of a button or through a simple REST API script.
So, start preparing today to defend your network against ransomware attacks. For more information on Echola’s fiber-cut switch VFC2011, don’t hesitate to contact sales@echola.com or visit www.echola.com.
Echola Systems Products Page: https://echola.com/products.html

One response to “Defending Lateral Movement of Ransomware Using a Fiber-Cut Kill Switch”
[…] Defending Lateral Movement of Ransomware Using a Fiber-Cut Kill Switch A Real Air Gap Defense Against Today’s Ransomware Attacks […]
LikeLike